A professional email list can look spotless in a spreadsheet and still behave like a bag of cracked lightbulbs once you start sending cold email. One wrong move, and the bounce rate spikes, replies dry up, and your domain reputation takes a hit that undermines sender reputation protection for weeks.
That’s why I treat Hunter.io email verification like a bouncer at the door to verify email address. It doesn’t just weed out obvious fakes, it helps me spot risky addresses before they cost me inbox placement. In this guide, I’ll show the exact workflow I use to validate a professional email list using Hunter.io, including how I prep my CSV, how I read the results, and how I segment the email list so I’m not guessing later.
What email verification protects, and where it still can’t save you
Email verification is about one thing: reducing preventable failure. I’m trying to avoid hard bounces from invalid email addresses, cut down on junk addresses, and protect my sender reputation before I run outreach or sync leads into a CRM.
Hunter’s own documentation frames email verification as an ongoing habit, not a one-time cleanup, and I agree. If you want the broader context (and why “unknown” results happen), Hunter’s email verification guide lays it out clearly. It explains how the email verifier checks MX records and the SMTP server to ensure validity.
Here’s the reality, though: no verifier can promise perfection. Some domains sit behind strict configurations, and some servers accept everything during the check (the “accept-all” problem). So instead of expecting magic, I use verification to make better decisions:
- I send confidently to valid email addresses that come back as deliverable.
- I pause and review borderline results (especially accept-all and unknown).
- I suppress anything that’s clearly invalid or disposable.
Pricing and plan names change, so I won’t anchor your process to a specific tier. Still, as of early 2026, Hunter includes a free plan with a small monthly credit allowance, and paid plans start around the low double-digits per month with higher credit pools. Verification typically consumes credits per check. I always confirm current limits inside my account before I run a large batch.
My step-by-step Hunter.io bulk email verifier workflow (CSV file to export)
I like predictable inputs because they lead to predictable outputs. Before I upload anything, I make my list boring in the best way: clean columns, consistent domains, and no duplicates.

Before I run a bulk check, I structure my CSV file with headers that make the export useful later. Here’s a simple format that works for outreach teams and for CRM imports:
| CSV file column header | What I use it for |
|---|---|
| The address Hunter will verify | |
| first_name | Personalization and merge fields |
| last_name | Deduping and CRM matching |
| company | Segmentation and routing |
| domain | Quick filtering (especially for catch-all domains) |
| source | Audit trail (where the lead came from) |
| notes | Manual context for the SDR or AE |
Then I run the bulk verification. Hunter’s UI labels can shift over time, but the flow stays similar across tools: upload, map fields, verify, export. This bulk email verifier (or email checker) makes it straightforward.
- Normalize the list first. I remove leading/trailing spaces, check email syntax, force lowercase emails, and delete obvious typos (like “gmal.com”).
- Kill duplicates early. If I’m verifying 10,000 rows, I don’t want to pay credits twice for the same mailbox.
- Upload the CSV file to Hunter’s verification area. I look for a bulk upload option, then map the email column if prompted.
- Run the verification job. For big files, I let it finish fully before I touch anything else.
- Export the results. I download a fresh CSV file with confidence scores and statuses, then I keep the original untouched. That way, I can always retrace my steps.
One small habit helps a lot: I add a timestamp column after export (like “verified_month”) so nobody treats last year’s check as current.
How I interpret results, then segment into send-safe, review, suppress
The export is where the real work starts for my outreach campaign. I don’t just filter for “valid” and call it done. Instead, I segment the list into three lanes that match real outreach campaign risk.
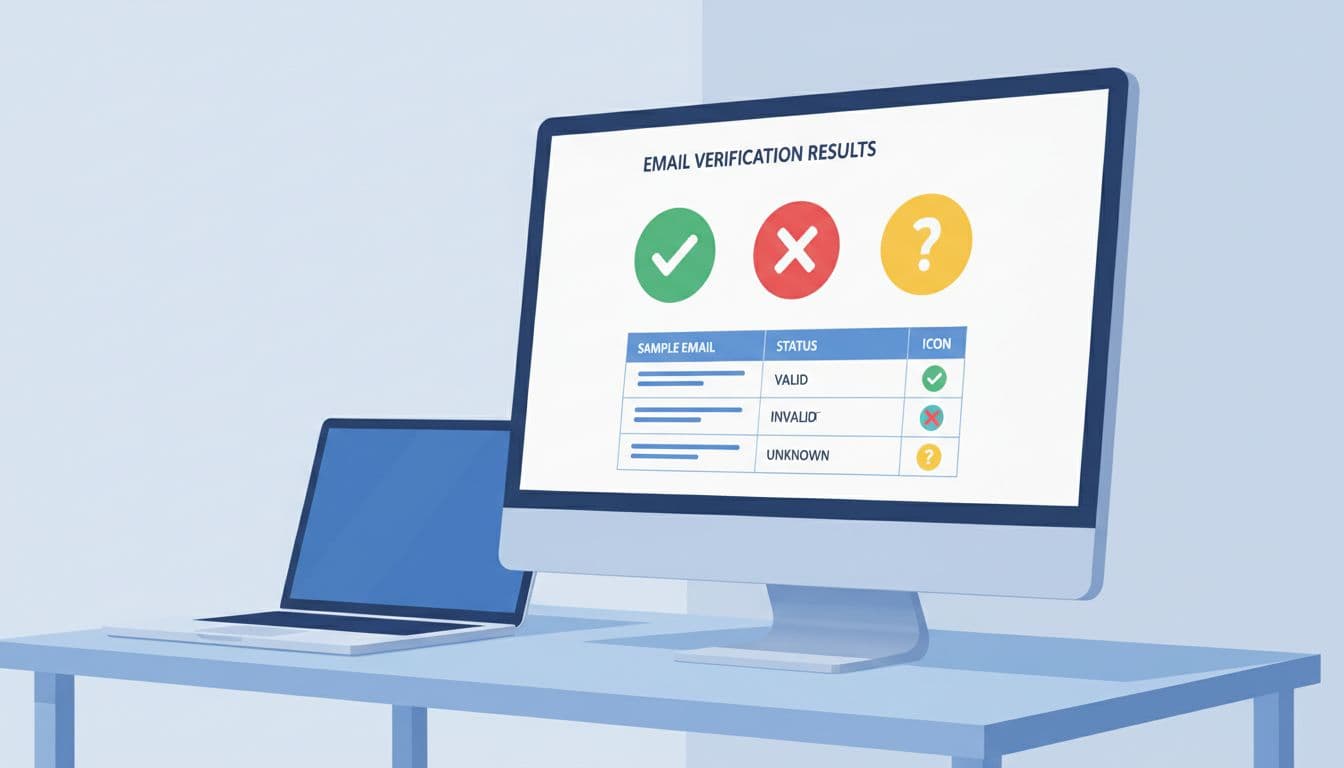
This table shows the decision logic I use, including SMTP checks and confidence scores. Exact status names can vary by provider and even by domain behavior, so I focus on the meaning and confidence score, not the label.
| Verification result (status or flag) | My segment | What I do next |
|---|---|---|
| Valid (deliverable) | Send-safe | Send with normal cadence and tracking |
| Invalid | Suppress | Never mail, remove from CRM sequences |
| Accept-all addresses (domain accepts all) | Review | Send only if high-value, start slow, watch bounces |
| Unknown (server didn’t confirm via SMTP check) | Review | Cross-check source, consider re-verify later |
| Disposable email address or temporary | Suppress | Exclude, often low intent and high risk |
| Role-based (info@, sales@) | Review | Use only when role outreach fits, personalize carefully |
| Webmail addresses (gmail/yahoo) | Review | Keep if expected (consultants), otherwise verify source |
Accept-all addresses aren’t “good” or “bad,” they’re “unproven.” I treat them like a lead that hasn’t picked up the phone yet.
Three common pitfalls show up in almost every B2B database I clean:
Role addresses can work, but they’re easy to overuse. If I’m selling to a team, “sales@” might be fine. If I’m targeting a decision-maker, it’s usually a dead end.
Disposable email addresses are a hard no for me. Even if one message lands, the long-term signal is messy, and it can distort campaign reporting.
Accept-all addresses are where teams get sloppy. I’ll still email them, but only after I tighten targeting, lower volume, and warm up the sending domain properly.
After segmentation, I also think about prevention. Instead of cleaning the same mess every quarter, I prefer verifying emails found via Hunter’s email finder and domain search at the point of capture. Hunter describes a practical approach to verifying submissions in real time with their API, and their guide on real-time email verification in forms is a good starting point.
If you’re comparing tools, I keep it simple: Hunter is strong when you want finding plus verification in one place, while other verifiers may fit better for pure high-volume validation. Hunter’s benchmark-style roundup, best email verifiers in 2026, is useful for framing trade-offs, and a third-party perspective like this Hunter.io review can help you sanity-check your pick.
Conclusion
When I validate professional email addresses using Hunter.io, I’m not chasing perfection, I’m reducing risk. Hunter.io email verification helps me protect deliverability, keep metrics honest, and stop bad addresses from poisoning good campaigns. The real win comes after the export, when I segment into send-safe, review, and suppress, then send with discipline. If your list is growing every week, the best time to verify is before you hit “send,” not after your bounce report arrives.